CAU Identity Management CIM
 Students Students |
 Employees Employees |
 Faculties Faculties |
 stud. Unions stud. Unions |
|---|
The introduction of identity management at Kiel University on the basis of a service agreement (in german) is intended to further develop and improve existing procedures for user and resource administration.
Why an identity management?
Identity management is used to centrally control access authorizations to IT systems, services and applications. The aim is to ensure that all students and employees at Kiel University will in future have automatic access to IT systems when they enrol or are hired, and that important required services are made available. As a result, many users will no longer need to renew their authorisation each year. Guests and partners of Kiel University are also to be given access to services via this system in a later step.
How does identity management work?
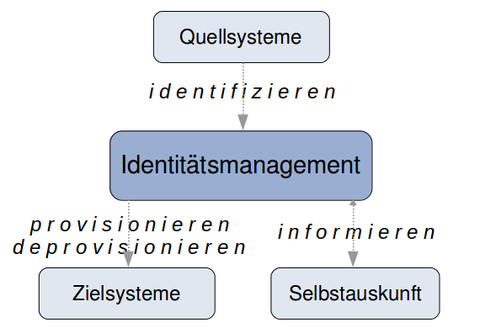
Identity management receives information about persons and roles from source systems (see graphic); these are 'identified'. Their entry and exit data is used to control access authorizations in the connected target systems. Access to systems and services is made possible on the basis of the entry date ('provisioned') or withdrawn ('deprovisioned') on the basis of the leaving date. Transparency is created by means of self-disclosure functions. Users can view ('inform') all data stored about them.
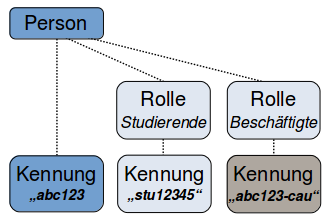
The CAU Identity Management (CIM) system includes the Campus Management System (HISinOne) for students and Personnel Management for employees at Kiel University as source systems. The CIM 'identifies' persons with their employee and student roles.
Connected target systems are the directory services Active Directory and OpenLDAP. Access authorizations to services (e.g. email services, WLAN, e-learning) are stored in these services when students are enrolled or employees begin their contracts. When a student is de-registered or an employee's contract ends, the stored authorizations are removed again.
In the computing centre and other institutions of Kiel University, the authorisations stored in the directory services can be used in future for logins (login, authentication) to IT systems, services and applications. The high degree of automation and updating of the CIM provides further advantages: The requirements for Kiel University to join DFN-AAI, the authentication and authorization infrastructure in the German Research Network, are fulfilled.
Single sign-on for web applications (Shibboleth)
By joining the DFN-AAI (Authentication and Authorization Infrastructure in the German Research Network), all members of Kiel University will be able to enter the 'single sign-on' world for federated web services. The technical prerequisites (Shibboleth) are in place for the cross-platform use of web-based applications through cooperation with other universities, with commercial and non-commercial partners. DFN-AAI 'creates the necessary relationship of trust as well as an organizational and technical framework for the exchange of user information' (https://www.aai.dfn.de/).
Kiel University has been a member of the DFN-AAI federation since May 2016.
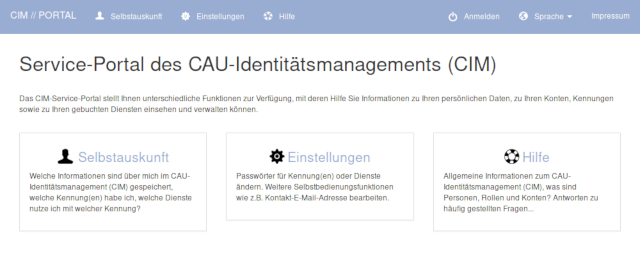
CIM Service Portal
The CIM Service Portal will in future be the central CIM entry point for all users. Here you will find important password functions and you can maintain your own personal contact data. In future, all users will also be able to see what data about them is stored in the CIM, in particular the validity period of each ID.
What changes, what remains?
The CIM introduction should be made as easy as possible for all computing centre users. Therefore, from the user's point of view, little will change at first: all previous RZ identifiers will remain valid, and all services and accesses associated with the previous RZ identifiers will be retained. So there is no need for action on the part of the users! Existing procedures for the administration of the computing centre users remain unchanged, changes in use must be applied for as before.
What is new is that the CIM assigns exactly one central identifier to each person, which should gradually replace existing ones as far as possible.
This person identification (CIM-ID) exists independently of the role assignment of the person (student or employee). Personal identifiers consist of 3 lower case letters and 3 digits (e.g. 'abc123'). Students still have their role identifier, the so-called stu-ID (e.g. 'stu12345'). If necessary, employees can also use their role identifier (e.g. 'abc123-cau').
These new identifiers will be used for 'single sign-on' accesses (see DFN-AAI) and for access to the CIM Service Portal immediately after their introduction. Step by step and as far as possible the personal identifiers will replace existing RZ identifiers.
Guests and partners
Employees of affiliated institutions and external cooperation partners are also subject to the existing procedures of the computing centre user administration. Changes of use as well as annual renewals - without a source system connection (see above) access authorizations are granted for a maximum of one year - are to be applied for as before.
Access to the CIM Service Portal is also possible for this group of employees using the existing RZ identifiers. For these identifiers, however, the prerequisites for a 'single sign-on' to federated services must be created by the person's home organisation.
Contact: idmadmin@rz.uni-kiel.de
Responsible
This list of responsible service supervisor is generated automatically.
